On smart contracts security
There’s no shortage in intros and roadmaps to smart contracts security, master the fundamentals, immediately test your hacker mindset. The fundamentals include what is a blockchain, how its vm executes transactions, and basic attack vectors.
This goal of this post is to answer, from a security researcher perspective: why become a smart contracts security researcher? and where to get started?
Why become a smart contracts security researcher?
There’s beauty to it
Smart contracts are code that handles funds. In the worst case scenario, the threat model is simple: steal those funds.
Blackhats have become increasingly sophisticated, often depleting contracts in a single well crafted transaction. In Yearn Finance hack, the attacker deployed attack contracts, executed the attack, and self destructed the contracts, all in one single transaction, stealing over $9M. Whitehats have a hard job here because with real funds at stake, a good whitehat must be as capable as the most sophisticated blackhat.
This piece is for hackers who are intrigued by the threat model of stealing funds, and being as capable as the most sophisticated blackhat. As long as hacks are still happening, there’s room for more whitehats.
It pays well
Top security researchers earn $500k+ per year, here’s an example from 2025.
Where to get started?
- Learn from previous hacks, like Yearn Hack.
- Take a free course at Cyfrin Updraft.
- Read technical posts at RareSkills.
Where to hunt for bugs and get paid? Two entry options there: either do bug bounties, or audit contests.
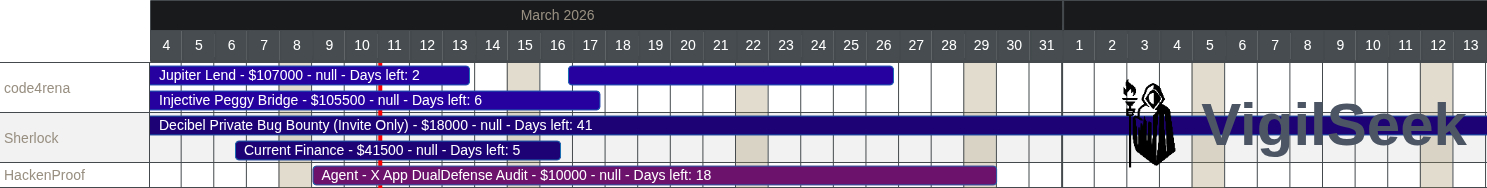 For checking live programs of bug bounties/contests, check out these aggregators: bug bounties, contests.
For checking live programs of bug bounties/contests, check out these aggregators: bug bounties, contests.